If you’re savvy enough to run a business with a website, you’re savvy enough to recognize business scams, right? Sure! You know, for example, that any email about a Nigerian prince who needs a loan (but will definitely pay it back later) is...bogus.
However, have you ever received an official-sounding email that highlights an “error 502” warning on one of your webpages? Or talks about “photo copyright violations”? If you’re not a web developer or an intellectual property lawyer, you might not know whether “error 502” should be a real concern or not. In this article, we will talk about how to spot scams, why they are dangerous, and how to arm yourself against them.
If an email is unsolicited but seems official, the first step is to stop and look closely at who sent the email. If you’re working with a professional web support team like ALINE, you should contact us directly about the email before clicking on any links or filling out any forms. Because we help keep many websites running safely and effectively, we see this type of email harassment more frequently than the average business owner. Using this article, you and your team can learn to swiftly identify the good from the bad. Below, we’ve tried to parse out our thought process as we determine valid from invalid in the world of online phishing.
How to Spot Phishy Emails
Whether their tone is casual or professional, emails with unsolicited links, forms, and attachments should give you pause. While the “you have an error 502 on some of your URL’s” is new, we’ve seen many emails about “photo copyright violations” and “impending web domain expirations” over the years.
When surveying an email, we look for the following red flags:
- The domain name from the sender is not the actual spoofed company’s domain (for example: sally@paypal-sender20044.com instead of sally@paypal.com).
- The domain name is misspelled (for example: sally@paypol.com instead of sally@paypal.com).
- There are grammatical and/or spelling mistakes. This shows that phishers are either looking for the most naive employees, or that they perhaps have a poor grasp of the English language, as many scams come from overseas.
- You have to open a link or attachment in order to understand the purpose of the email. (For example, you could get this note from an unknown person: “Can you resend this invoice? Attached below.”)
- As you open a file, you receive a pop-up warning about the file’s legitimacy or the application asks you to adjust your settings. That’s a good moment to stop and reassess!
- The email has a sense of urgency. (For example, “Act now or it will be too late,” or “You may lose service if you don’t update your account now.”)
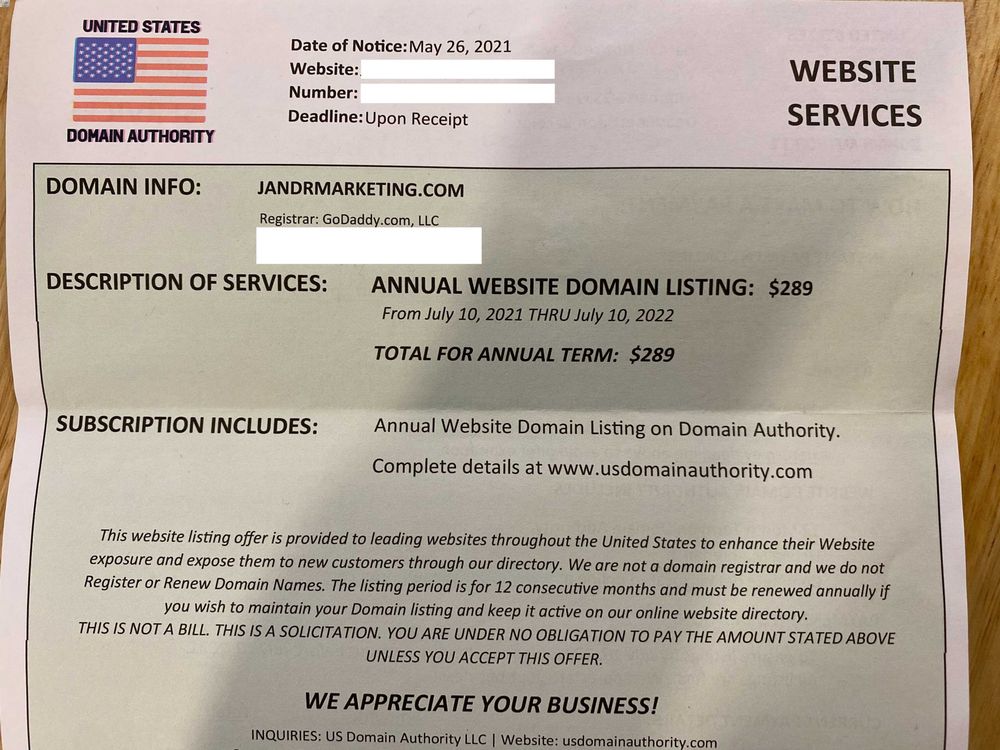
Sometimes these letters and emails can seem fairly official. Check out this actual letter that we received recently:
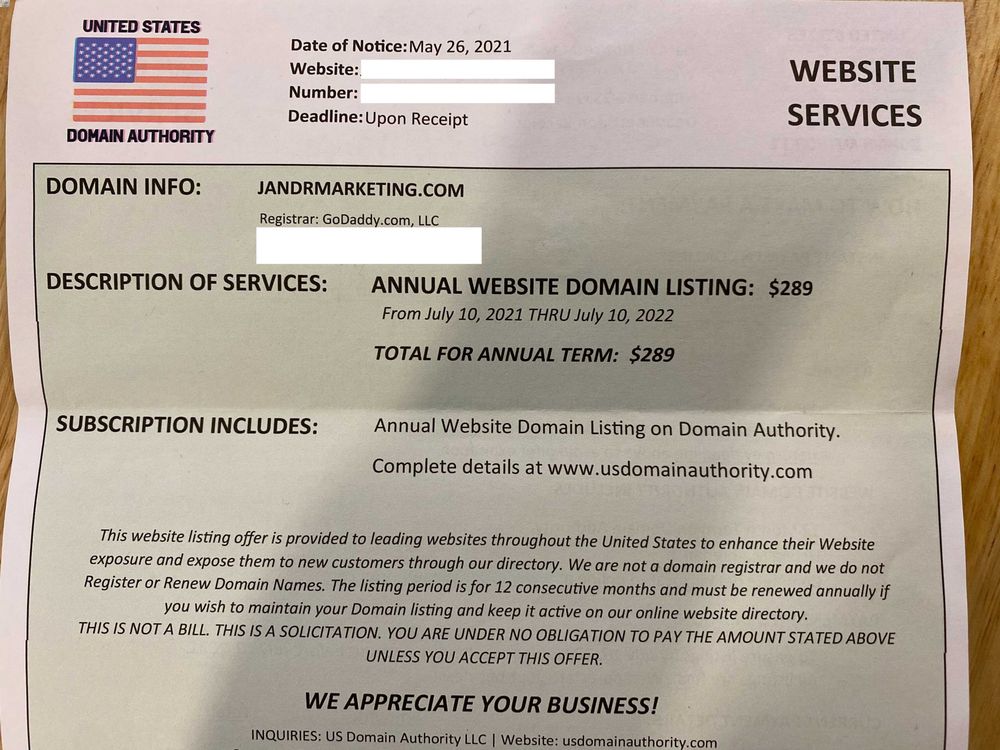
Would you have paid this “bill”? It looks pretty convincing, but when you type “usdomainauthority.com” into your browser, it says the site does not exist. If you see this or any of the other flags, notify your team not to click on any links or engage with the email.
What Is the Danger?
Links and form-fills can install malicious software, spyware, or a virus onto a device. Even worse, these programs can run behind the scenes, and are thus undetectable to the user. Clients who fall for these scams should immediately change their password and call their IT professional.
A phisher can use a harmless scam to watch a user’s email interactions and figure out who identifies scams and alerts others. In a future scam, the phisher will avoid the more astute observers.
Once any malware has been installed, it can harvest your sensitive information, send out more phishing messages to contacts in your address book or provide a cyber-criminal with remote access to your device.
Phishing text messages and emails have become an unavoidable threat these days. Your best protection is to err on the side of caution and use the “delete” button on emails and texts that seem sketchy.
How to Prepare Yourself for Email Scams
A real company will never ask you to share personal information via insecure channels like email or text. If the message is truly important, the sender will use verifiable methods like telephone or snail mail. In all cases, you can do some proactive sleuthing by reaching out to the company via another channel, independent of the email and links or forms.
If you think you’ve clicked on a bad link or form-fill, use this helpful step-by-step guide that www.agingcare.com put together for their clients. It does not assume a high level of technical knowledge, and shows you when to reach out for more help.
If ALINE is your web host, you know we’ll never ask for sensitive information by sending a pushy email. Our research shows that there is no way to fully block these types of emails. The best thing for you to do if you get a form-fill or email from an unknown source about anything related to your website content or functionality is to delete it. If something looks strange from someone that you do trust, then reach out to them outside of that email and make sure that they actually sent it. (They could have been hacked and not know that their account is being used for scams.)
Also, please keep us in the loop. If you’ve seen a new type of scam come across your desk and want to warn others, we’d love to know and pass the message on. That way more businesses, both large and small, can better protect themselves.